OSINT: Open Source Intelligence
If you’ve heard the name but are wondering what it means, OSINT stands for open source intelligence, which refers to any information that can legally be gathered from free, public sources about an individual or organization. In practice, that tends to mean information found on the internet, but technically any public information falls into the category of OSINT whether it’s books or reports in a public library, articles in a newspaper or statements in a press release.

What is OSINT used for…
By gathering publicly available sources of information about a particular target an attacker — or friendly penetration tester — can profile a potential victim to better understand its characteristics and to narrow down the search area for possible vulnerabilities. Without actively engaging the target, the attacker can use the intelligence produced to build a threat model and develop a plan of attack. Targeted cyber attacks, like military attacks, begin with reconnaissance, and the first stage of digital reconnaissance is passively acquiring intelligence without alerting the target.
Reconnaissance is a type of computer attack in which an intruder engages with the targeted system to gather information about vulnerabilities. The attacker for instance, first discovers any vulnerable ports by using software’s like port scanning.
Gathering OSINT on yourself or your business is also a great way to understand what information you are gifting potential attackers. Once you are aware of what kind of intel can be gathered about you from public sources, you can use this to help you or your security team develop better defensive strategies. What vulnerabilities does your public information expose? What can an attacker learn that they might leverage in a social engineering or phishing attack?
What is the OSINT framework?
This is a cybersecurity framework with a collection of OSINT tools to make your intel and data collection tasks easier. This tool is mostly used by security researchers and penetration testers for digital foot-printing, OSINT research, intelligence gathering, and reconnaissance. It provides a simple web-based interface that allows you to browse different OSINT tools filtered by categories.
It also provides an excellent classification of all existing intel sources, making it a great resource for knowing what info sec areas you are neglecting to explore, or what will be the next suggested OSINT steps for your investigation.
OSINT Framework is classified based on different topics and goals. This can be easily seen while taking a look at the OSINT tree available through the web interface OSINT Framework.

OSINT framework classifications
When you immediately load the website you’ll notice the OSINT tree is before your eyes on the left side of your screen.
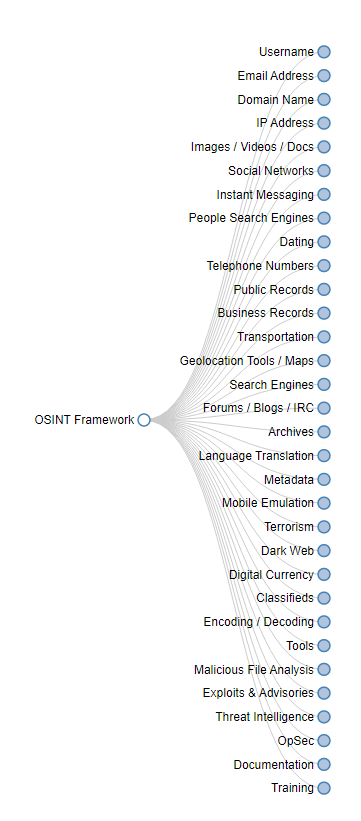
OSINT Tree
There are some highlights you should know; take a look at the following indicators on the right side, for some of the listed tools:
- (T) — Indicates a link to a tool that must be installed and run locally
- (D) — Google Dork (aka Google Hacking)
- (R) — Requires registration
- (M) — Indicates a URL that contains the search term and the URL itself must be edited manually.
When you click any of the categories, such as Username, Email Address, or Domain Name, a lot of useful resources will appear on the screen, in the form of a sub-tree.
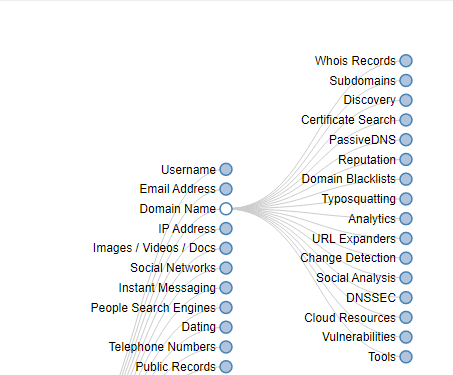
Domain Name sub-tree
Searching for users, email addresses, IP addresses or social network details becomes super easy as you have all the tools available in one single interface. It’s just like a giant OSINT bookmarks library.
For example, within IP Address, specifically through the Protected by Cloud Services section, you will find links to CloudFlare Watch and CloudFail.
The same happens with other popular categories such as Email Address — Breach Data you will find many links to useful resources such as Have I been pwned? or DeHashed.
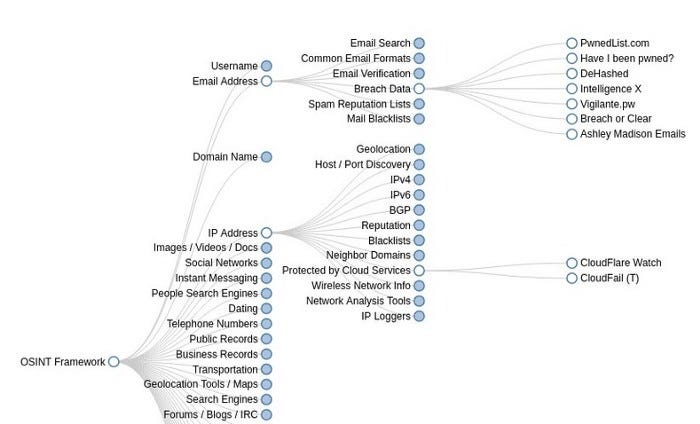
OSINT Framework classification
Do you need to identify phone numbers? There are a lot of phone number tracking tools that allow you to identify an incoming call. These include:
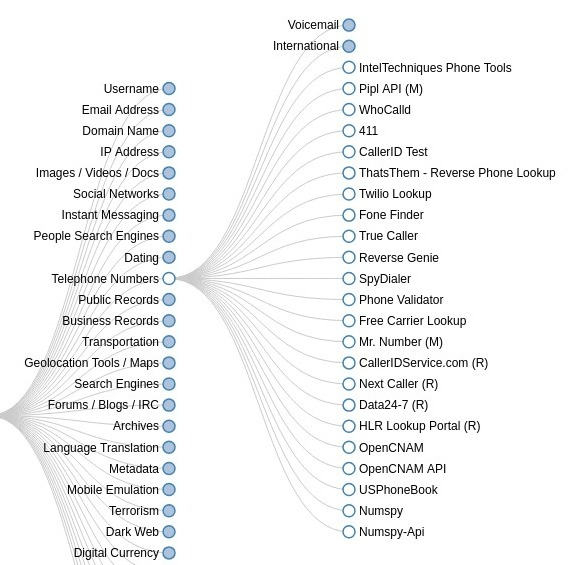
Telephone numbers Verification
Other OSINT tools are found in Kali Linux penetration testing distribution which are:
Kali Linux Tools on OSINT
Conclusion
As you can see by browsing the OSINT Framework website, there are almost unlimited ways to get data about any target you’re investigating. Plus, this framework can be used as a good cybersecurity checklist to see what areas you have left to explore while analyzing any individual or company.
For anyone involved in cybersecurity, understanding how to collect open source intelligence is a vital skill. Whether you’re defending an enterprise network or testing it for weaknesses, the more you understand about its digital footprint the better you are to see it from an attacker’s point of view. Armed with that knowledge, you can then go on to develop better defensive strategies.
This article has been written by Amol Rangari, a Cyber Security Specialist who believes that a secure cyberspace is a result of individual contributions.
